Question 1
Most-appropriate topic codes (IBDP Computer Science):
• Topic 1.2 — System design
▶️ Answer/Explanation
Answer:
1. Graphical User Interface (GUI) elements like menus or toolbars.
2. Command Line Interface (CLI) or dialogue boxes for user input.
Detailed Solution:
An application interface is essentially the bridge between the software and the person using it, dictating how interactions happen. When you open a program, the visual elements you rely on—like the Graphical User Interface (GUI) featuring windows, icons, menus, and pointers (WIMP)—are primary features of this interface. Additionally, features like toolbars provide quick access to frequently used functions, while dialogue boxes prompt users for specific inputs or confirmations. Some software might also include a Command Line Interface (CLI) for users who prefer typing text-based instructions rather than clicking around. Ultimately, these features are meticulously designed to make software navigation intuitive, accessible, and user-friendly, ensuring that tasks can be executed efficiently.
Question 2
Most-appropriate topic codes (IBDP Computer Science):
• Topic 3.1 — Networks
▶️ Answer/Explanation
Answer:
To securely access a private network over a public network by encrypting the transmitted data, preventing unauthorized access.
Detailed Solution:
A Virtual Private Network (VPN) is primarily utilized to create a secure, encrypted “tunnel” over a fundamentally unsecure medium like the public internet. By routing your data through this encrypted connection, it ensures that sensitive information—such as corporate documents or login credentials—remains completely private and protected from potential eavesdroppers, hackers, or even your Internet Service Provider. This technology is especially vital for remote workers who need to securely access their company’s internal servers and databases from a coffee shop or their home office. Furthermore, because a VPN masks the user’s actual IP address and replaces it with one from the VPN server, it allows individuals to bypass geographical restrictions and maintain a higher level of anonymity online.
Question 3
Most-appropriate topic codes (IBDP Computer Science):
• Topic 1.1 — Systems in organizations
▶️ Answer/Explanation
Answer:
1. They allow data collection from a large user base quickly and cost-effectively.
2. They offer anonymity, which often leads to more honest and unbiased feedback from users.
Detailed Solution:
When a systems analyst is trying to figure out what a new or updated computer system needs, surveys present an incredibly efficient data-gathering tool. One major advantage is their scalability; you can digitally distribute a survey to hundreds or thousands of employees across the globe in seconds, making it far cheaper and faster than scheduling individual interviews. Because the questions are standardized, the resulting quantitative data is also much easier to analyze using software, highlighting common trends quickly. Another significant benefit is that surveys can be completely anonymous, which removes the pressure users might feel in a face-to-face setting, encouraging them to provide highly honest, critical feedback about the current system’s flaws without fear of reprimand.
Question 4
Construct a logic diagram for the following expression:
$X = \text{NOT } A \text{ OR } B \text{ AND NOT } C$
Most-appropriate topic codes (IBDP Computer Science):
• Topic 2.1 — Computer organization
▶️ Answer/Explanation
Answer: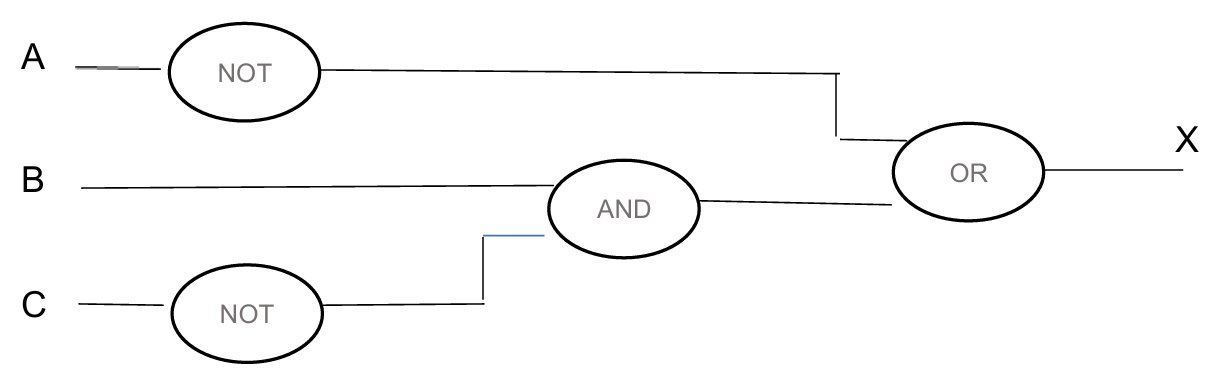
Detailed Solution:
To accurately construct this logic diagram, it is crucial to follow the strict order of Boolean operations, which prioritizes NOT, then AND, and finally OR. You start by drawing your three distinct input lines labeled A, B, and C on the left. First, you pass input A through a standard NOT gate to generate the $\text{NOT } A$ signal, and similarly pass input C through a NOT gate to generate $\text{NOT } C$. Next, you take the raw input B and connect it, along with the output from the $\text{NOT } C$ gate, into an AND gate. This yields the intermediate expression $B \text{ AND NOT } C$. For the final step, you route both the $\text{NOT } A$ signal and the output from your AND gate into a single OR gate. The resulting line exiting this final OR gate represents your complete output $X$.
Question 5
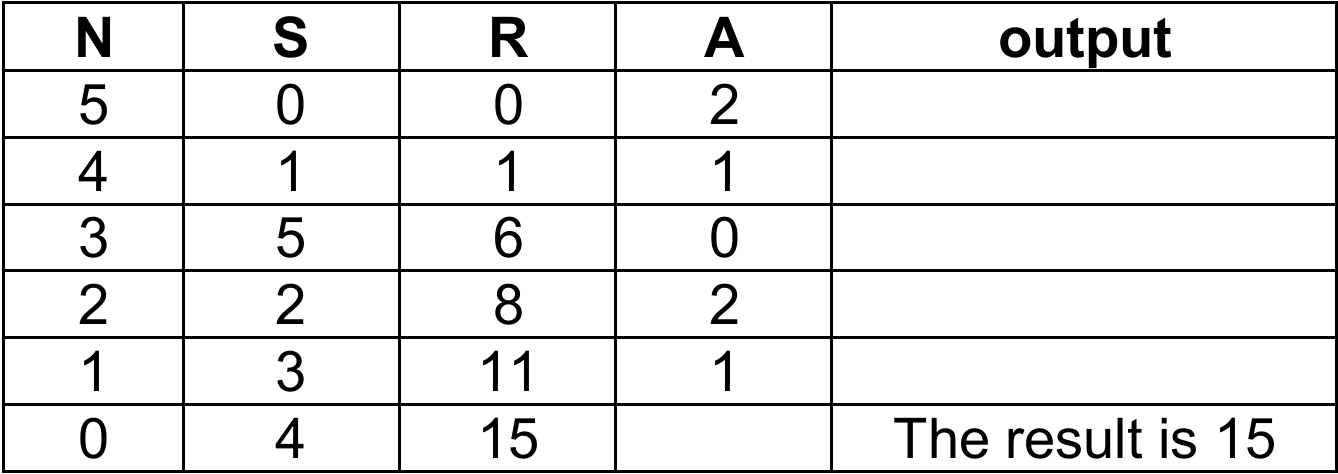
Construct a trace table for the following algorithm:
$S = 0$
$R = 0$
loop while $N > 0$
$A = N \text{ mod } 3$
if $A = 0$
then
$S = S – N$
else
if $A = 1$
then
$S = S + N$
else
$S = S + 1$
end if
end if
$R = R + S$
$N = N – 1$
end loop
output (‘The result is ‘, R)
Most-appropriate topic codes (IBDP Computer Science):
• Topic 4.2 — Connecting computational thinking and program design
▶️ Answer/Explanation
Answer:
Detailed Solution:
Tracing an algorithm requires meticulously tracking the state of each variable as you step through the logic row by row. We initialize our variables with $N=5$, $S=0$, and $R=0$. In the first iteration, $N$ is 5, so $A$ evaluates to $5 \text{ mod } 3$, which is 2. Since $A$ is neither 0 nor 1, the nested ‘else’ triggers, causing $S$ to increment by 1 (becoming 1), $R$ to become 1, and $N$ to drop to 4. As we loop again with $N=4$, $A$ becomes 1, triggering the first ‘else-if’ branch, which adds $N$ (4) to $S$, making $S=5$ and updating $R$ to 6. This careful, step-by-step evaluation of the modulo operation determines exactly how $S$ updates in each cycle—whether subtracting $N$, adding $N$, or adding 1. After 5 full cycles, $N$ reaches 0, the loop safely terminates, and the final accumulated value inside $R$, which is 15, is output to the screen.
Question 6
Most-appropriate topic codes (IBDP Computer Science):
• Topic 1.1 — Systems in organizations (Implementation)
▶️ Answer/Explanation
Answer:
1. Direct changeover.
2. Parallel running.
Detailed Solution:
When a business is ready to push a newly developed computer system into live operation, they must choose a strategic implementation method to minimize disruption. One common approach is a direct changeover, where the company unplugs the old system and immediately switches entirely to the new one on a specific date; it’s fast and inexpensive but carries a high risk of catastrophic failure if bugs are present. An alternative is parallel running, where both the legacy system and the new system run simultaneously for a set period. While this requires double the data entry and is significantly more expensive, it offers a massive safety net because the organization can always fall back on the reliable old system if the new one encounters critical issues.
Question 7
Most-appropriate topic codes (IBDP Computer Science):
• Topic 3.1 — Networks
▶️ Answer/Explanation
Answer:
It acts as the internet’s directory by translating human-readable domain names into numerical IP addresses.
Detailed Solution:
The internet is fundamentally a massive network of machines communicating via numerical identifiers known as Internet Protocol (IP) addresses. However, humans are generally terrible at remembering long strings of numbers, preferring simple text like ‘google.com’. The primary role of a Domain Name System (DNS) server is to act as a colossal, automated phonebook that bridges this gap. When you type a URL into your browser, the DNS server instantly looks up that domain name and translates it into the corresponding IP address. This critical translation allows your computer to locate the correct web server somewhere in the world and retrieve the website data you requested seamlessly behind the scenes.
Question 8
A binary number is held in the following 12-bit register:
![]()
(a) State the hexadecimal representation of this binary number.
(b) State how many different binary numbers can be represented in a 12-bit register.
Most-appropriate topic codes (IBDP Computer Science):
• Topic 2.1 — Computer Organization
▶️ Answer/Explanation
(a) F3A
To convert the 12-bit binary number to hexadecimal, it must be partitioned into groups of four bits starting from the rightmost side (the least significant bit). The register displays the bits as 111100111010, which separates into 1111, 0011, and 1010. Using the standard conversion weightage where the bits represent $8, 4, 2, 1$, the group $1111$ evaluates to $(1 \times 8) + (1 \times 4) + (1 \times 2) + (1 \times 1) = 15$, which is the character F in hexadecimal. The next group $0011$ evaluates to $(0 \times 8) + (0 \times 4) + (1 \times 2) + (1 \times 1) = 3$. The final group $1010$ evaluates to $(1 \times 8) + (0 \times 4) + (1 \times 2) + (0 \times 1) = 10$, which corresponds to the character A. Therefore, reading the hexadecimal characters from left to right gives the final representation F3A.
(b) $4096$ (or $2^{12}$)
The total number of distinct binary combinations a register can hold is determined by the fundamental exponential formula $2^n$, where $n$ represents the number of bit positions available. Since each individual bit is a binary digit that can exist in only one of two distinct states (either a logical 0 or a logical 1), the total unique permutations across 12 bits are calculated by multiplying 2 by itself 12 times. This calculation $2^{12}$ mathematically equals 4096. This number defines the complete range of values the register can represent, starting from the binary value for decimal 0 all the way up to the maximum value of binary 111111111111.
Question 9
An architect uses a single computer for her business. She uses hand-drawn sketches to present her ideas to clients and computer-aided design (CAD) software to create construction projects, alterations, and redevelopments.
(a) (i) State what is meant by CAD software.
(ii) Outline two benefits for the architect of using CAD software.
The architect often creates large graphic files that are sent via the internet.
(b) Explain the need for data compression software in storing and transferring these large graphic files.
Data loss can cause downtime, which can force the architect to pause business operations. The impact on productivity depends on the amount of data lost as well as the time it takes for data recovery.
(c) (i) Describe how the architect could minimize downtime if the disk system on her computer fails.
(ii) Outline two causes of data loss other than hardware failure.
Most-appropriate topic codes (IBDP Computer Science):
• Topic 1.1 — Systems in organization
▶️ Answer/Explanation
(a)(i)
For the correct answer:
Software used to create, modify, or optimize precision technical drawings and models.
CAD (Computer-Aided Design) software is a specialized digital tool that replaces manual drafting with an automated, mathematically precise process. It allows the architect to construct technical drawings using a coordinate system, defining vectors and geometric entities such as lines, arcs, and splines to represent real-world objects with exact scaled dimensions.
(a)(ii)
For the correct answer:
1. Allows for quick and easy modifications without redrawing.
2. Enables 3D rendering for better client visualization.
The first benefit is parametric editing, where a change to a single parameter (like a wall length) automatically updates all related views and sections, saving immense time compared to erasing physical pencil lines. The second benefit is the generation of photorealistic 3D models and walkthroughs using rendering algorithms that simulate lighting and materials, transforming abstract 2D plans into a visceral experience that clients without technical knowledge can easily understand and approve.
(b)
For the correct answer:
Compression reduces the massive file sizes, saving local hard drive space and significantly decreasing the bandwidth and time required to upload/download files over the internet.
CAD files, especially those with embedded raster images or complex 3D meshes, contain vast amounts of redundant data; compression algorithms use techniques like LZW (Lempel-Ziv-Welch) for lossless reduction in vector files or discrete cosine transform for lossy compression in embedded images. Mathematically, a compression ratio defined as $\text{Ratio} = \frac{\text{Uncompressed Size}}{\text{Compressed Size}}$ quantifies the efficiency, where a higher ratio means fewer bytes are transmitted. This reduction is critical because the time to transfer data over a network connection with a limited bitrate $R$ (in bits per second) is given by $t = \frac{\text{File Size}}{R}$, so shrinking the file directly minimizes latency and prevents internet transfer timeouts, while also lowering the cost per gigabyte of cloud or physical storage.
(c)(i)
For the correct answer:
She could implement a RAID (Redundant Array of Independent Disks) configuration or maintain daily cloud backups to quickly restore data.
To minimize the debilitating downtime from a disk failure, the architect should adopt a proactive disaster recovery strategy centered on redundancy. A mirrored RAID setup (like RAID 1) stores identical data onto two physical drives simultaneously; when one fails, the system can instantly and transparently failover to the surviving disk without any interruption to her operating system or CAD applications. Alternatively, integrating an automated daily cloud backup synchronizes her latest project revisions to a geographically separate data center, allowing for a full system image restore onto a new drive in a matter of hours, significantly shrinking the recovery time objective (RTO).
(c)(ii)
For the correct answer (any two):
Malicious software (like ransomware or viruses) and human error (like accidentally deleting files).
One primary non-hardware threat is malware, particularly ransomware, which uses public-key cryptography to encrypt the architect’s files; the data becomes mathematically irretrievable without a decryption key that only the attacker possesses, essentially destroying her business assets unless a clean backup exists. Another pervasive cause is accidental deletion or overwriting by the user, a simple human error where critical CAD drawing files are emptied from the recycle bin or a new, blank version is saved over a completed complex project, instantly destroying weeks of intricate design work.
Question 10
A school has a local area network (LAN) with a central server that stores many files containing personal, health, and financial information. The LAN is used by the following types of user: network administrators, teachers, students and guests.
(a) Explain how the different levels of access for the users of this LAN could be implemented.
(b) (i) Suggest one communications link that would provide high-speed internet access for the school.
(ii) Suggest two measures to protect the school’s LAN from external network security threats.
The school gives students and teachers their own school email account.
(c) List three problems that might result from providing email access to all students and teachers.
Most-appropriate topic codes (IBDP Computer Science):
• Topic 3.1 — Networks
• Topic 1.1 — Systems in organization
▶️ Answer/Explanation
(a)
For the correct answer:
By setting up user accounts with unique usernames and strong passwords, organizing these accounts into logical user groups (such as administrators, teachers, students, and guests), and then assigning specific access rights or permissions (read, write, execute, delete) to files and folders on the central server based on group membership.
The central server authenticates each user at login, verifying their identity against a stored credentials database. Once authenticated, the operating system’s access control list (ACL) mechanism determines what actions that user—or their group—can perform on each protected resource. For example, network administrators might be granted full control over all directories to manage backups and security policies, teachers could have read and write access to curriculum folders and student grade databases but no access to sensitive financial records, students might receive read-only access to shared learning materials and a personal write-enabled home directory, while guests are restricted to a heavily limited profile with only internet access and no visibility of internal server files. This hierarchical, role-based access control ensures confidentiality and integrity of the stored personal, health, and financial information.
(b)(i)
For the correct answer:
A fibre-optic cable connection (or fibre-optic broadband).
A fibre-optic link uses strands of glass or plastic to transmit data as pulses of light, offering exceptionally high bandwidth and significantly lower latency compared to traditional copper-based connections like DSL. For a school environment where hundreds of users may simultaneously stream educational videos, access cloud-based applications, and transfer large files, the symmetric upload and download speeds of a dedicated fibre-optic connection prevent congestion and ensure reliable, high-speed internet access throughout the entire LAN.
(b)(ii)
For the correct answer (any two):
1. Installing and properly configuring a hardware firewall (or a software firewall on the server).
2. Deploying a proxy server to filter web traffic and hide internal IP addresses.
3. Implementing a robust intrusion detection/prevention system (IDS/IPS).
4. Using a demilitarised zone (DMZ) for any public-facing services.
A hardware firewall is placed at the network perimeter between the school’s LAN and the external internet connection; it examines all incoming and outgoing data packets, applying predefined security rules to block unauthorised access attempts, port scans, and malicious traffic before they reach internal devices. A proxy server acts as an intermediary for requests from clients seeking resources from external servers—it can be configured to block access to known malicious websites, filter inappropriate content, cache frequently accessed data to improve performance, and mask the internal IP addresses of school workstations, making it harder for external attackers to map the network topology. These measures, when combined, create a layered defence strategy against external threats such as hackers, malware, and denial-of-service attacks.
(c)
For the correct answer (any three):
1. Increased vulnerability to phishing attacks and malware distribution via email attachments or malicious links, which could compromise the entire LAN.
2. Instances of cyberbullying or harassment among students using school-provided email accounts, raising safeguarding and legal concerns.
3. Wasted network and server storage resources due to large attachments, spam accumulation, or excessive personal use.
4. Distraction from educational activities during class time if students use email for non-academic communication.
5. Increased administrative overhead for IT staff who must manage account provisioning, password resets, and acceptable-use policy violations.
Providing email access to all students and teachers, while educationally beneficial, significantly expands the attack surface of the school’s network. A single student who unknowingly clicks a phishing link can introduce ransomware that encrypts critical files on the central server, causing widespread data loss and operational disruption. The anonymity and ease of digital communication also create avenues for cyberbullying, where harmful messages can be sent repeatedly and reach victims even outside school hours, potentially leading to severe psychological harm and legal liability for the institution. Furthermore, without strict monitoring and quota systems, the email platform can quickly become clogged with non-essential messages and large multimedia attachments, consuming finite storage space on the server, degrading network performance for genuine academic tasks, and diverting valuable IT staff time away from infrastructure maintenance toward routine user support issues.
Question 11
There are 200 students in a school. Their names are held in the one-dimensional string array STUDENTS. The one-dimensional integer array MARKS stores marks (0-100 inclusive) that students scored in an examination.
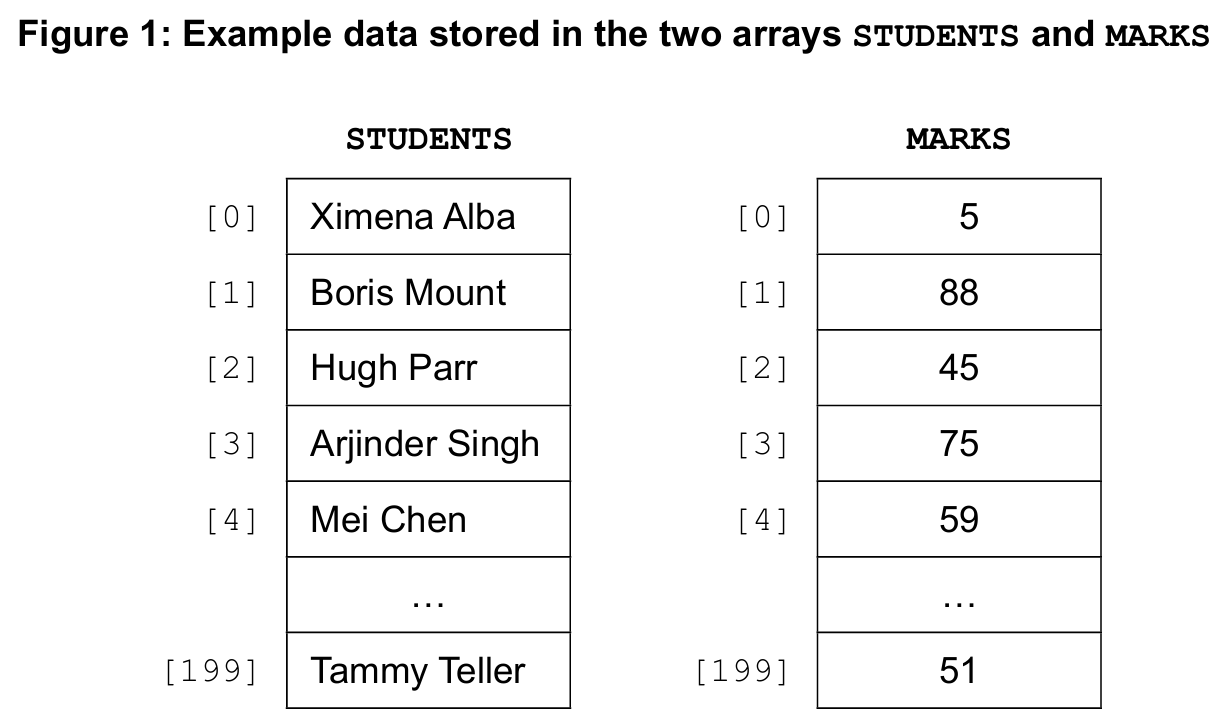
The one-dimensional integer array GRADES will be used to store the grades awarded to students based on their examination marks. In Figure 1, Boris Mount scored 88 marks. His grade will be stored in GRADES.
Consider the following algorithm that the school currently uses for awarding grades:
GRADES [K] = 1 + (MARKS [K] div 10)
if GRADES [K] >= 7 then
GRADES [K] = 7
end if
end loop
(a) (i) Determine the value of GRADES [0].
(ii) Determine the value of GRADES [1].
(iii) Determine the value of GRADES [2].
(iv) State the minimum mark necessary to achieve Grade 7.
Grade 1 is a failing grade. Each student who receives a failing grade must re-sit the examination.
(b) Construct an algorithm in pseudocode to fill the one-dimensional string array RESIT with the names of students who must re-sit the examination.
A different method of awarding grades is proposed for the examinations. This new grading system will use three grades represented by the letters A, B, and C. Grades A, B, or C will be calculated as follows:
– The average mark for all students is calculated.
– Grade A is awarded if an individual student’s marks are more than 20 marks above the average mark for all students.
– Grade B is awarded if an individual student’s marks are within 20 marks of the average mark for all students.
– Grade C is awarded if an individual student’s marks are more than 20 marks below the average mark for all students.
For example, if the average mark for all students is 49.5: Grade A is awarded if a student’s marks are greater than 69.5. Grade B is awarded if a student’s marks are in the range from 29.5 to 69.5 inclusive. Grade C is awarded if a student’s marks are less than 29.5.
(c) Construct an algorithm in pseudocode to calculate and store the letter grades of all students in the one-dimensional string array LETTERGRADES as described.
Most-appropriate topic codes (IBDP Computer Science):
• Topic 4.3 — Introducton to programming
▶️ Answer/Explanation
(a)(i)
For the correct answer:
1
Looking at the extract from Fig. 1, the student at index 0, Aarav Arora, scored a mark of 5. The algorithm calculates the initial grade using the formula $\text{GRADES}[K] = 1 + (\text{MARKS}[K] \text{ div } 10)$. Since $5 \text{ div } 10$ equals 0 in integer division, the expression evaluates to $1 + 0 = 1$. The subsequent conditional check, $\text{if GRADES}[K] \ge 7$, is false for this value, so the grade remains unchanged at 1.
(a)(ii)
For the correct answer:
7
The student at index 1, Boris Mount, achieved a mark of 88, as explicitly shown in the question stem. Substituting this into the formula gives $\text{GRADES}[1] = 1 + (88 \text{ div } 10)$, which is $1 + 8 = 9$. The algorithm then checks the condition $\text{if GRADES}[K] \ge 7$. Since 9 is indeed greater than or equal to 7, the grade is forcibly capped and reassigned to the maximum value of 7 before the loop ends for this index.
(a)(iii)
For the correct answer:
5
Based on the visible data in the array extract, Chi-Chi Wang at index 2 has a mark of 47. Applying the same grading rule, the computation is $1 + (47 \text{ div } 10)$, which simplifies to $1 + 4 = 5$. As the resulting grade of 5 does not satisfy the condition $\ge 7$, the conditional statement’s body is skipped, and the final stored value in GRADES[2] is directly set to 5.
(a)(iv)
For the correct answer:
60
To achieve Grade 7, a student must either have the formula yield a value of 7 or higher before capping, or directly cause the cap to activate. Since any value $\ge 7$ gets rounded down to 7, we need the initial calculation $1 + (\text{MARKS} \text{ div } 10)$ to be at least 7. This means $\text{MARKS} \text{ div } 10$ must be at least 6. The smallest integer mark that results in a quotient of 6 under integer division is $60$, as $60 \div 10 = 6$ exactly.
(b)
For the correct answer:
Algorithm for RESIT array.
To construct the RESIT array, a new index counter, such as `COUNT`, must be initialized to 0 to manage the consecutive filling of the new array. A loop iterates through all 200 student records from `K = 0` to `199`. Inside the loop, a selection statement checks if the condition `GRADES[K] == 1` is true. If it is, the student’s name from `STUDENTS[K]` is assigned to the next available position `RESIT[COUNT]`, and `COUNT` is immediately incremented to prepare for the next potential failing student.
(c)
For the correct answer:
Algorithm for LETTERGRADES array.
This algorithm requires two distinct passes through the data. The first pass is a sequential accumulation loop that sums the `MARKS[K]` of every student into a variable `SUM`. Once the total is computed, the floating-point average `AVG` is calculated by dividing the sum by 200. The second pass then loops through all indices again, comparing each student’s mark to the thresholds derived from the average. The boundaries are strictly defined: a mark strictly greater than $\text{AVG} + 20$ earns an “A”, a mark strictly less than $\text{AVG} – 20$ gets a “C”, and any mark falling within the inclusive range $[\text{AVG} – 20, \text{AVG} + 20]$ is assigned a “B”.
